NewStarCTF-FirstWeek
RE
#begin
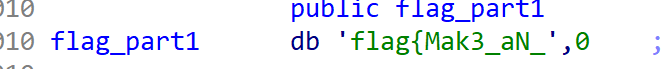
拖进IDA打开,跟随指引即可看到flag1
shift+F12可看到flag2

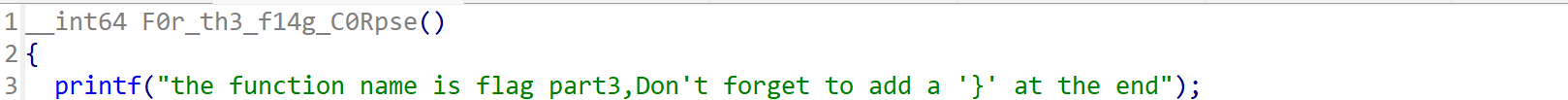
flag3为函数名
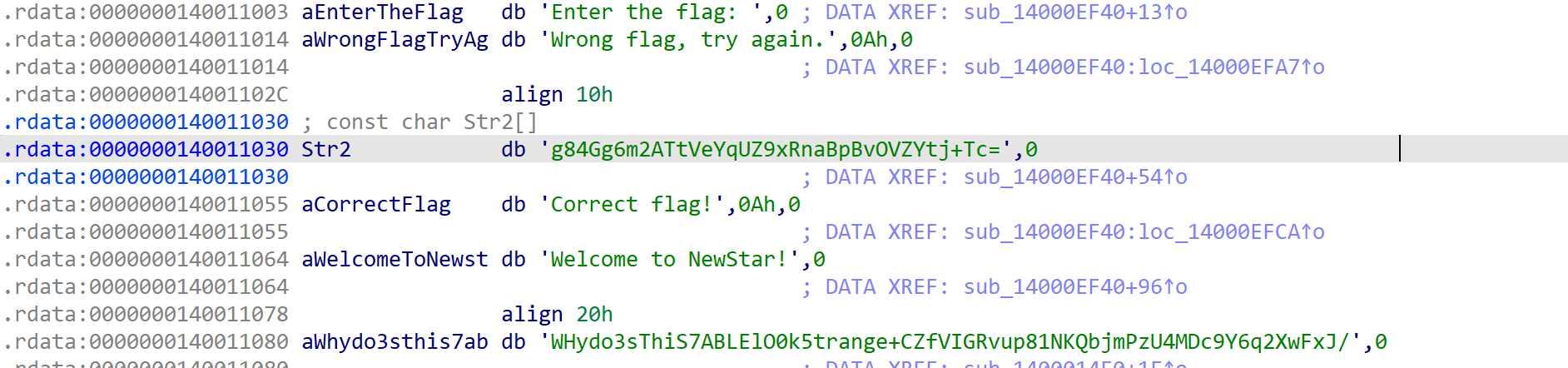
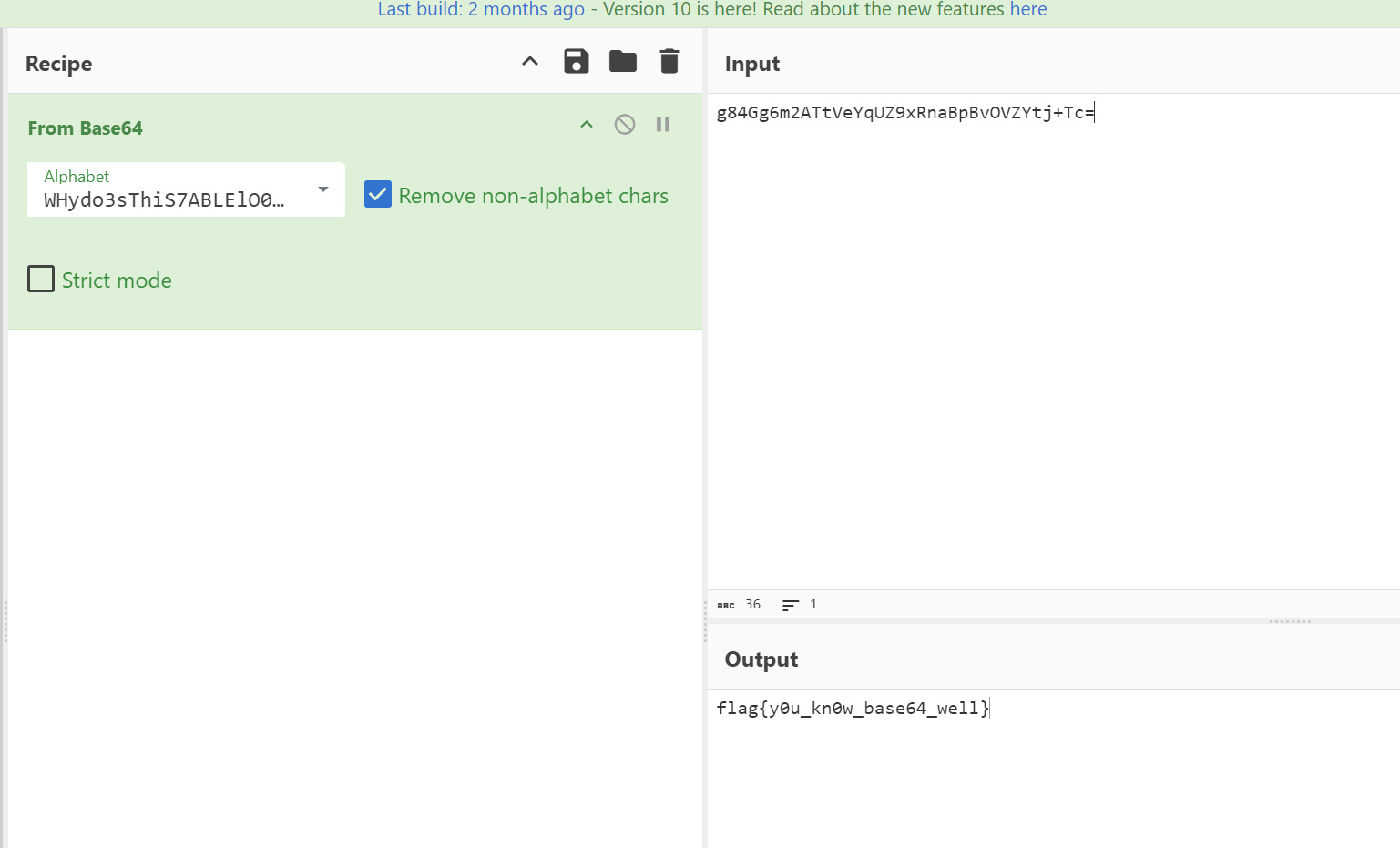
#bsae64
shift+F12,一眼base64换表
厨子梭哈
#ezAndroidStudy
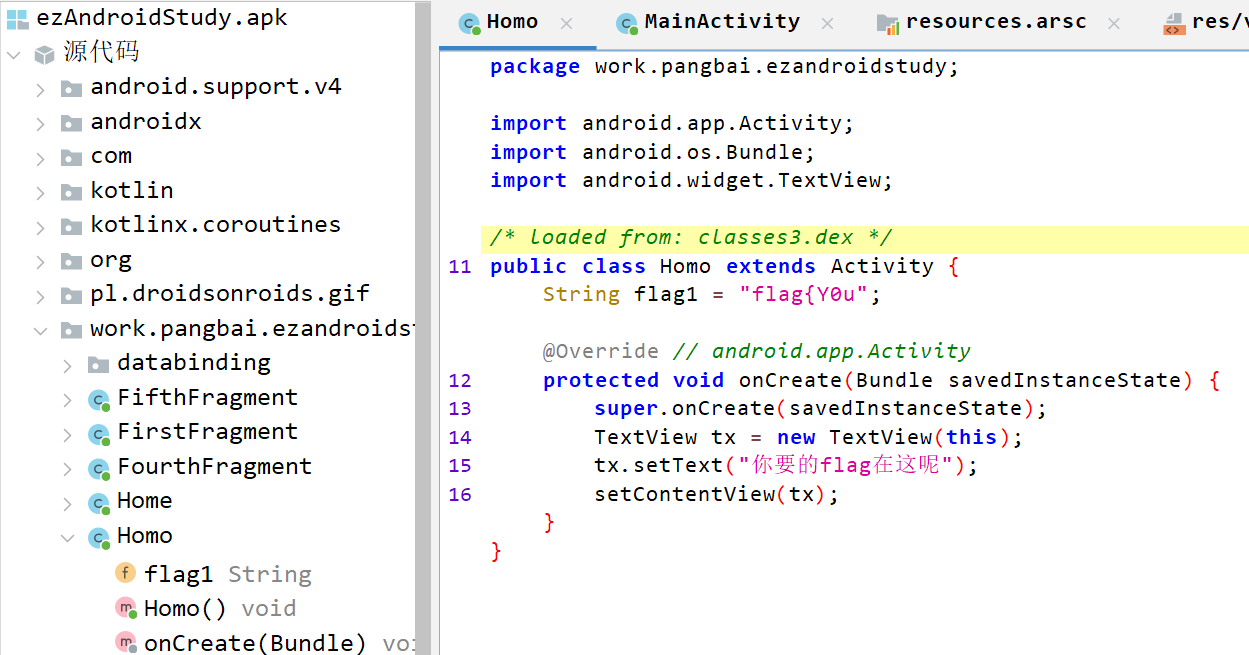
第一段直接找即可
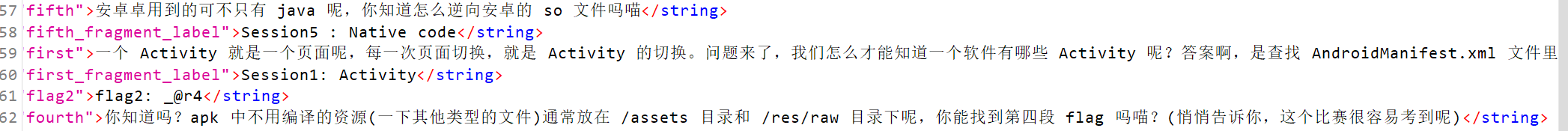
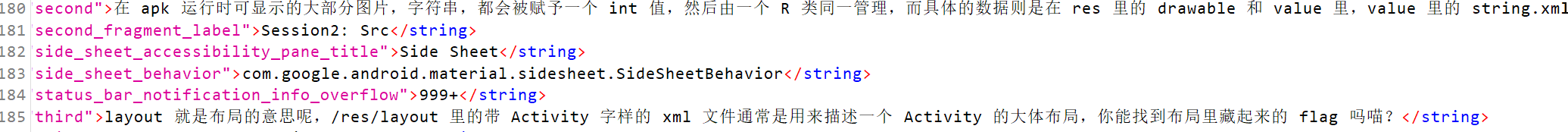
根据string的提示,我们可以找到flag2,3,4
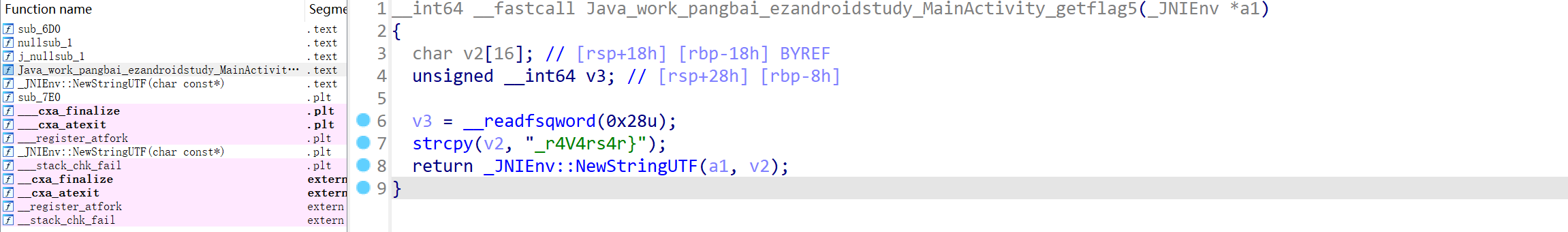
第五段由提示知在so文件里面 ida反编译后打开:
#Simple_encryption
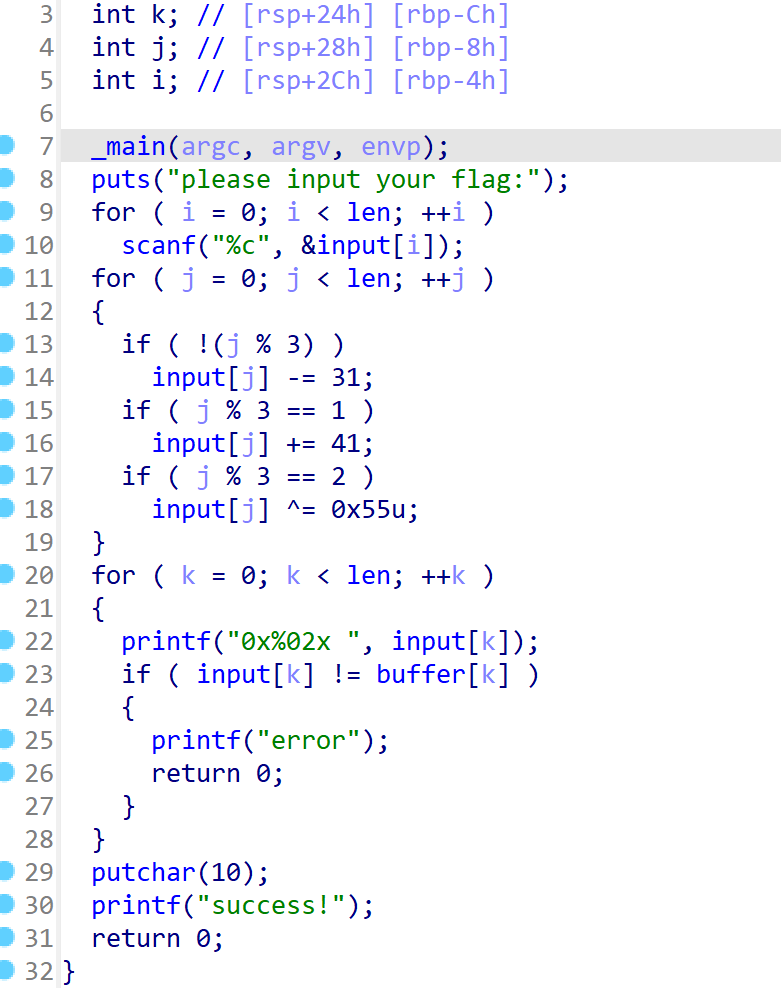
很简单的逻辑,不必多说: 1
2
3
4
5
6
7
8
9
10
11
12
13
14enc = [0x47, 0x95, 0x34, 0x48, 0xA4, 0x1C, 0x35, 0x88, 0x64, 0x16, 0x88, 0x07,
0x14, 0x6A, 0x39, 0x12, 0xA2, 0x0A, 0x37, 0x5C, 0x07, 0x5A, 0x56, 0x60,
0x12, 0x76, 0x25, 0x12, 0x8E, 0x28]
for i in range(len(enc)):
if i % 3 == 0:
enc[i] += 31
if i % 3 == 1:
enc[i] -= 41
if i % 3 == 2:
enc[i] ^= 0x55
flag = ''
for i in range(len(enc)):
flag += chr(enc[i])
print(flag)
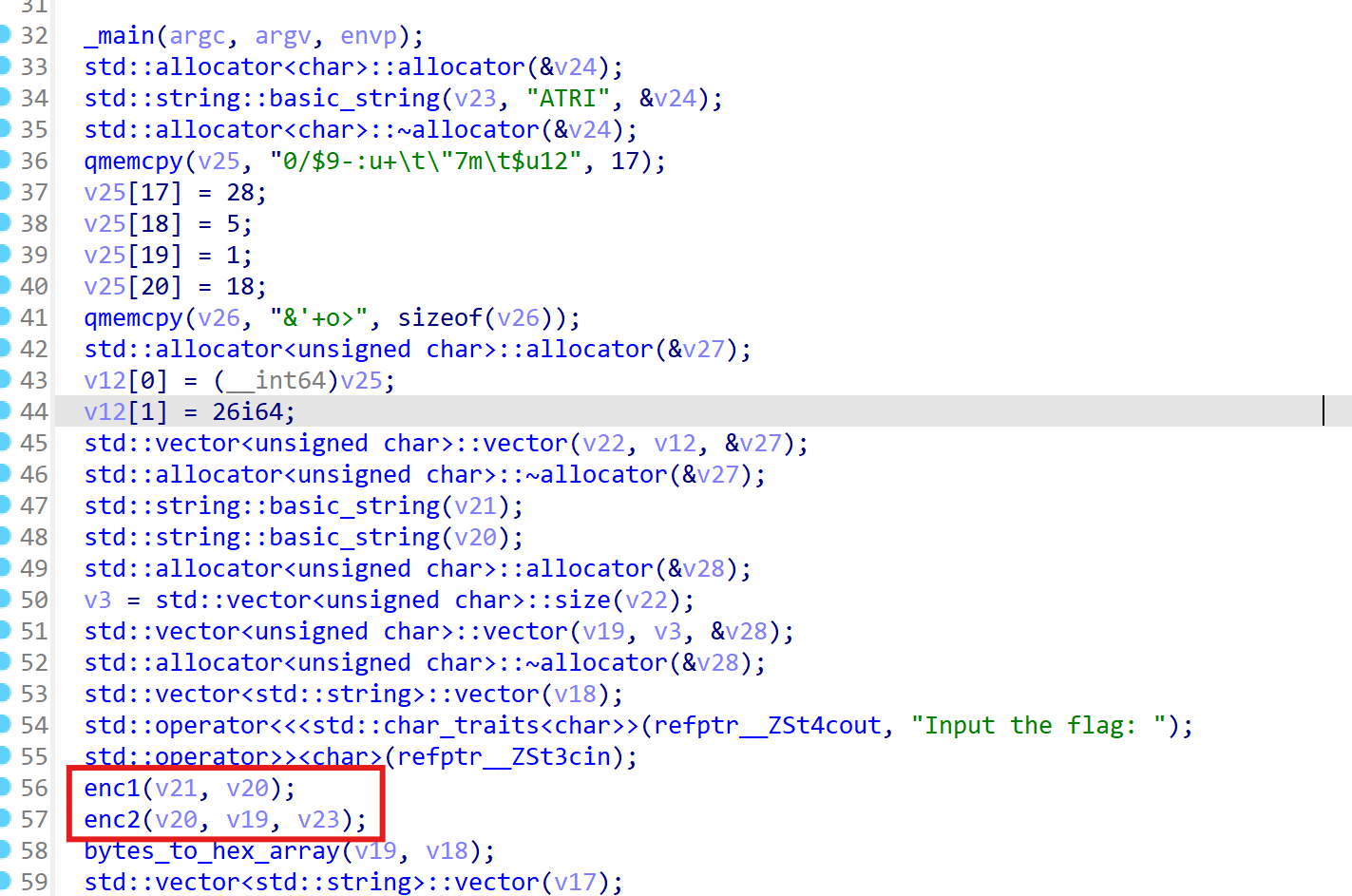
两个很简单的加密: 动调之后,容易发现逻辑,代码如下:
1
2
3
4
5
6
7
8
9
10key = "ATRI"
enc = [0x30, 0x2F, 0x24, 0x39, 0x2D, 0x3A, 0x75, 0x2B, 0x09, 0x22,
0x37, 0x6D, 0x09, 0x24, 0x75, 0x31, 0x32, 0x1C, 0x05, 0x01,
0x12, 0x26, 0x27, 0x2B, 0x6F, 0x3E]
enc1 = []
flag = ''
for i in range(len(enc)):
enc1.append(enc[i] ^ ord(key[i % 4]) ^ 0x17)
flag += chr(enc1[i])
print(flag)
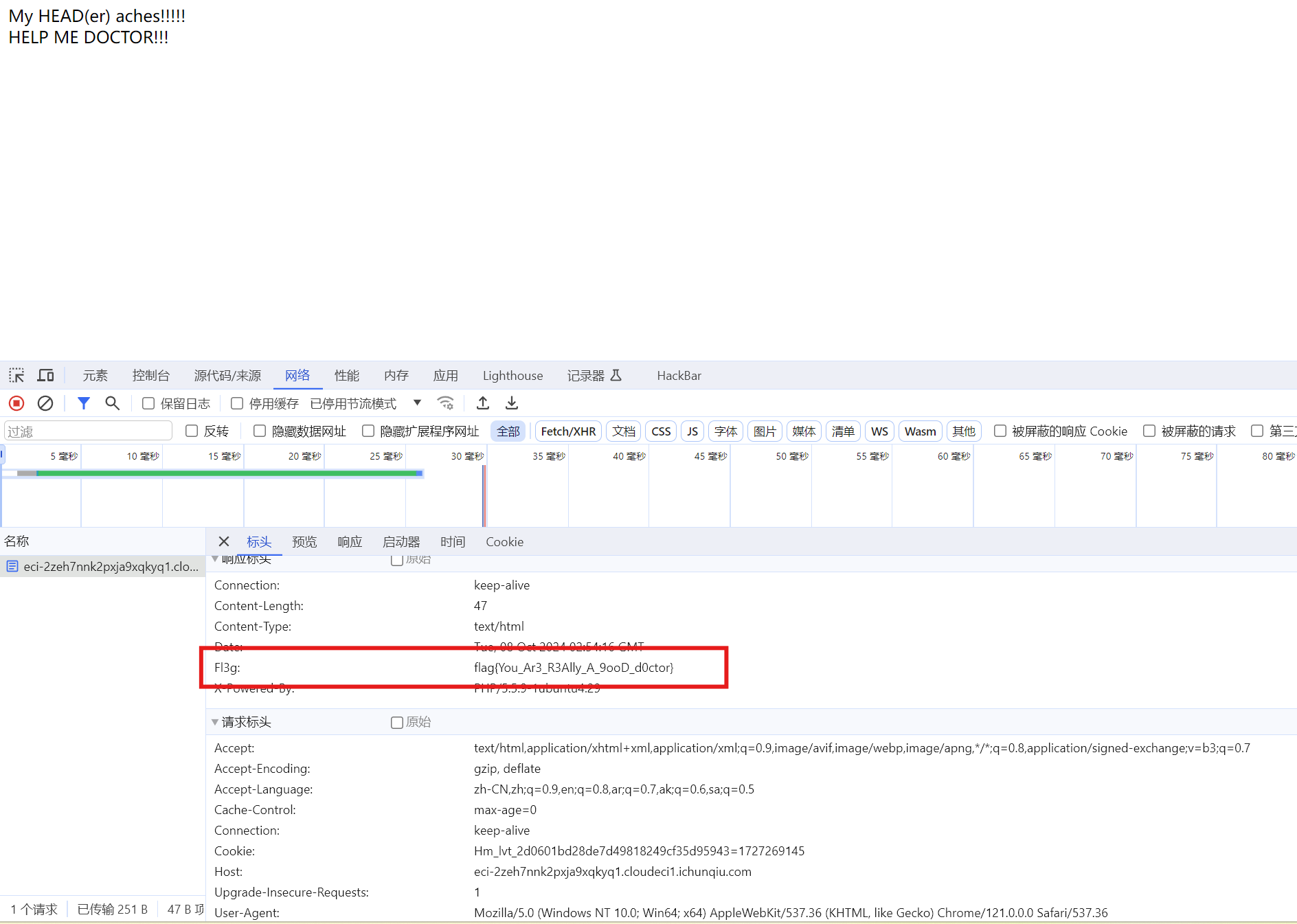
WEB
#headach3
打开环境,网络中查看,一眼顶真
CRYPTO
#xor
很简单的逻辑: 1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20# from pwn import xor
# #The Python pwntools library has a convenient xor() function that can XOR together data of different types and lengths
# from Crypto.Util.number import *
#
# key = b'New_Star_CTF'
# flag='flag{*******************}'
#
# # m1 = bytes_to_long(bytes(flag[:13], encoding='utf-8'))
# # m2 = flag[13:]
#解密脚本:
from pwn import xor
from Crypto.Util.number import *
c1= 8091799978721254458294926060841
c2= b';:\x1c1<\x03>*\x10\x11u;'
m1 = c1 ^ bytes_to_long(key)
m2 = xor(key, c2)
print('m1=',long_to_bytes(m1))
print('m2=',m2)
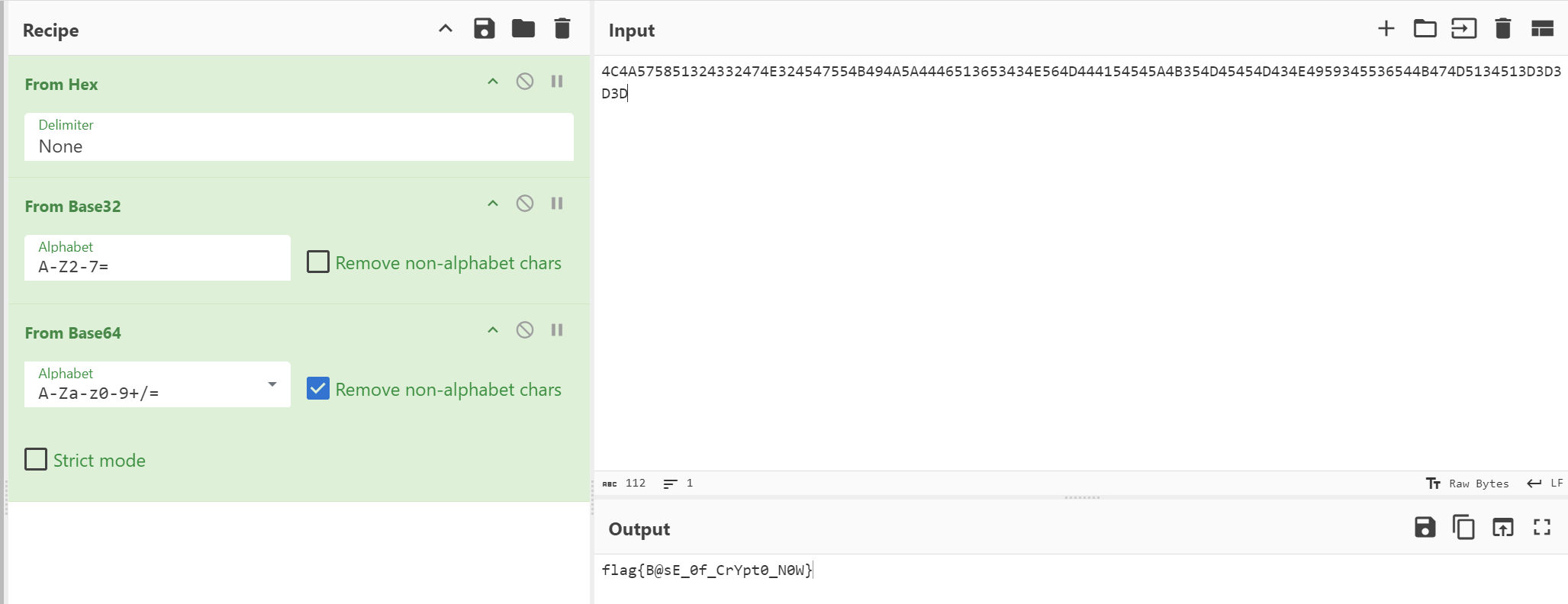
#一眼秒了
由题的描述可知,n过小,可以肢解分解,在factordb.com上直接分解。
之后就是正常的rsa了 1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25# from Crypto.Util.number import *
# from gmpy2 import *
# from serct import flag
# p = getPrime(512)
# q = getPrime(512)
# n = p*q
# m = bytes_to_long(flag)
# e = 65537
# c = powmod(m, e, n)
# print(n)
# print(c)
# '''
# n = 52147017298260357180329101776864095134806848020663558064141648200366079331962132411967917697877875277103045755972006084078559453777291403087575061382674872573336431876500128247133861957730154418461680506403680189755399752882558438393107151815794295272358955300914752523377417192504702798450787430403387076153
# c = 48757373363225981717076130816529380470563968650367175499612268073517990636849798038662283440350470812898424299904371831068541394247432423751879457624606194334196130444478878533092854342610288522236409554286954091860638388043037601371807379269588474814290382239910358697485110591812060488786552463208464541069
# '''
n = 52147017298260357180329101776864095134806848020663558064141648200366079331962132411967917697877875277103045755972006084078559453777291403087575061382674872573336431876500128247133861957730154418461680506403680189755399752882558438393107151815794295272358955300914752523377417192504702798450787430403387076153
c = 48757373363225981717076130816529380470563968650367175499612268073517990636849798038662283440350470812898424299904371831068541394247432423751879457624606194334196130444478878533092854342610288522236409554286954091860638388043037601371807379269588474814290382239910358697485110591812060488786552463208464541069
p = 7221289171488727827673517139597844534869368289455419695964957239047692699919030405800116133805855968123601433247022090070114331842771417566928809956044421
q = 7221289171488727827673517139597844534869368289455419695964957239047692699919030405800116133805855968123601433247022090070114331842771417566928809956045093
e = 65537
phi = (p - 1) * (q - 1)
d = invert(e, phi)
m = pow(c,d,n)
print(long_to_bytes(m))1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20def caesar_encrypt(plaintext, shift):
encrypted_text = ""
for char in plaintext:
if char.isalpha():
base = 'A' if char.isupper() else 'a'
encrypted_char = chr((ord(char) - ord(base) + shift) % 26 + ord(base))
encrypted_text += encrypted_char
else:
encrypted_text += char
return encrypted_text
plaintext = "ksjr{EcxvpdErSvcDgdgEzxqjql}"
encrypted = []
shift = 21
for i in range(len(plaintext)):
encrypted.append(caesar_encrypt(plaintext[i], shift))
shift -= 2
print("Encrypted:", encrypted)




