SHCTF-Week1WP
RE
#ezxor
shift+F12,查找字符串,
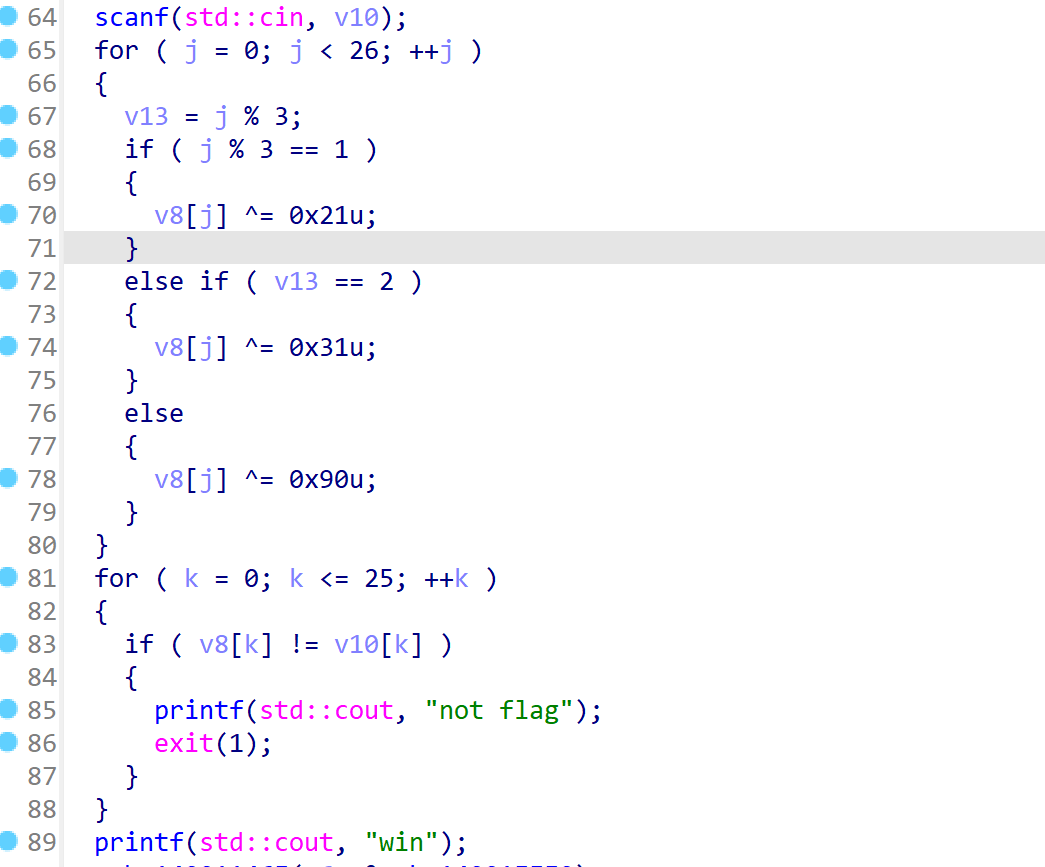
很简单的逻辑 1
2
3
4
5
6
7
8
9
10
11
12
13
14
15enc = [0xC3, 0x69, 0x72, 0xC4, 0x67, 0x4A, 0xE8, 0x11, 0x43, 0xCF,
0x6F, 0x00, 0xF3, 0x44, 0x6E, 0xF8, 0x59, 0x49, 0xE8, 0x4E,
0x5E, 0xE2, 0x53, 0x43, 0xB1, 0x5C]
flag = ''
for i in range(len(enc)):
if i % 3 == 1:
enc[i] ^= 0x21
elif i % 3 == 2:
enc[i] ^= 0x31
else:
enc[i] ^= 0x90
flag += chr(enc[i])
print(flag)1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
245 3 0 0 7 0 0 0 0
6 0 0 1 9 5 0 0 0
0 9 8 0 0 0 0 6 0
8 0 0 0 6 0 0 0 3
4 0 0 8 0 3 0 0 1
7 0 0 0 2 0 0 0 6
0 6 0 0 0 0 2 8 0
0 0 0 4 1 9 0 0 5
0 0 0 0 8 0 0 7 9
|
|
5 3 4 6 7 8 9 1 2
6 7 2 1 9 5 3 4 8
1 9 8 3 4 2 5 6 7
8 5 9 7 6 1 4 2 3
4 2 6 8 5 3 7 9 1
7 1 3 9 2 4 8 5 6
9 6 1 5 3 7 2 8 4
2 8 7 4 1 9 6 3 5
3 4 5 2 8 6 1 7 9
<!-- shctf{468912723481342575971422657913948591537428763345261} -->
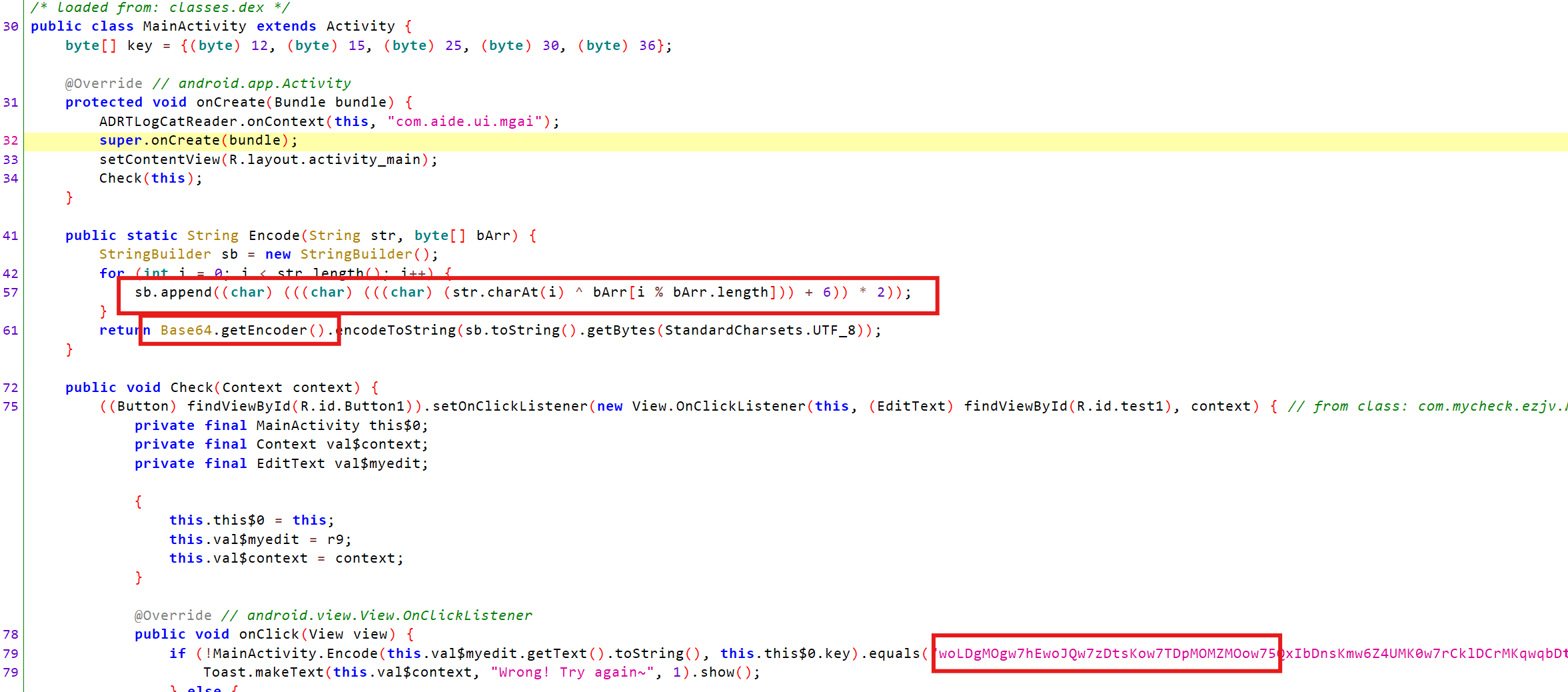
然后我们直接上脚本即可 1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18import base64
key = [12, 15, 25, 30, 36]
encoded_string = "woLDgMOgw7hEwoJQw7zDtsKow7TDpMOMZMOow75QxIbDnsKmw6Z4UMK0w7rCklDCrMKqwqbDtMOOw6DDsg=="
def decode(encoded_str, key):
decoded_bytes = base64.b64decode(encoded_str)
decoded_str = decoded_bytes.decode('utf-8')
# print(decoded_str)
decrypted_chars = []
for i, char in enumerate(decoded_str):
original_char = chr(((ord(char) // 2) - 6) ^ key[i % len(key)])
decrypted_chars.append(original_char)
return ''.join(decrypted_chars)
original_string = decode(encoded_string, key)
print("解密后的字符串:", original_string)
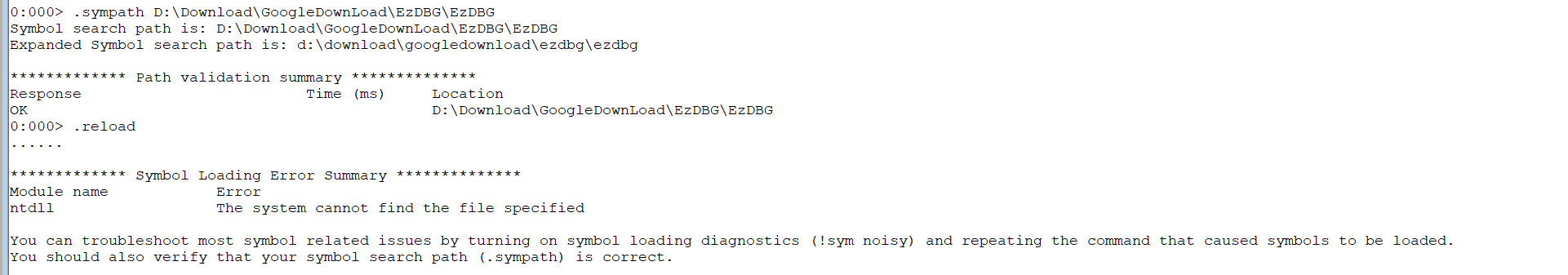
x EzDBG!main //找main函数地址
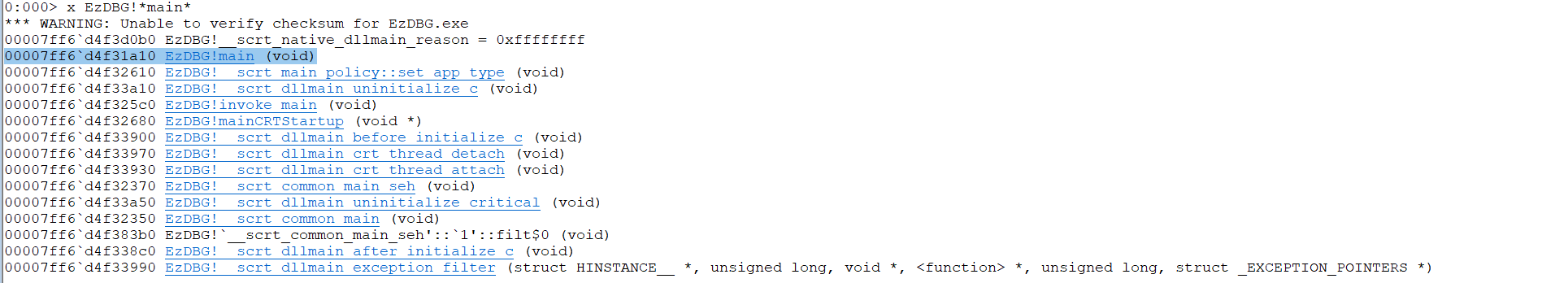
u 0x00007ff6d4f31a10 L100 //反汇编mian函数,然后分析知enc与0x66异或
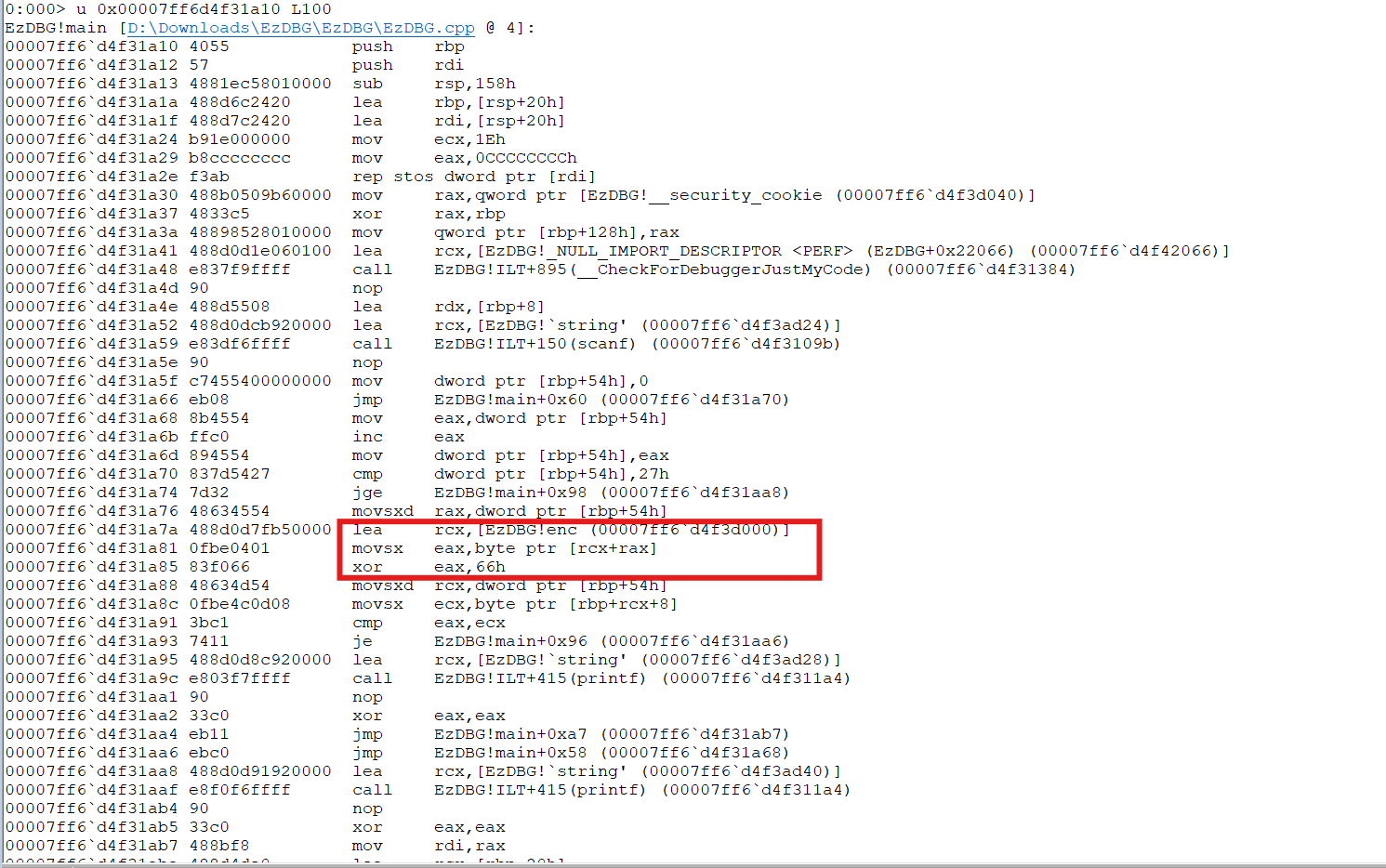
dd 00007ff6d4f3d000 //查看enc数组
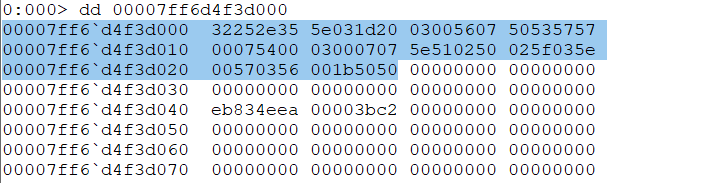
上脚本 1
2
3
4
5
6
7enc = [0x35, 0x2e, 0x25, 0x32, 0x20, 0x1d, 0x03, 0x5e, 0x07, 0x56, 0x00, 0x03, 0x57, 0x57, 0x53, 0x50,
0x00, 0x54, 0x07, 0x00, 0x07, 0x07, 0x00, 0x03, 0x50, 0x02, 0x51, 0x5e, 0x5e, 0x03, 0x5f, 0x02,
0x56, 0x03, 0x57, 0x00, 0x50, 0x50, 0x1b]
flag = ''
for i in range(len(enc)):
flag += chr(enc[i] ^ 0x66)
print(flag)1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38# from Crypto.Util.number import *
# from gmpy2 import*
# # from flag import flag
# flag = b"********************"
# m = bytes_to_long(flag)
# p = getPrime(1024)
# q = next_prime(p)
# n = p * q
# e = 0x10001
# d = inverse(e, (p-1) * (q-1))
# c = pow(m, e, n)
# print(c)
# print(d)
# '''
# c = 10125001938741182874131434694053378894804175034333902925514888331755677063642938643541979182051668124386228365867007880044490715315905869250481987164228878653341801956850989531329839208326074075528123949149274715167422406616246088956811606499279927381665136698802510232361039936017310673376593400290986619596933813134120555625242111739485364703291029899201832727105148017303746551843238803178316593187195896900279416883471647073533378463894407062054229713313651602345845508284470911670805747883737287349748165429142274116638239804130451999211604713028677235482320836574787852928109589514256905251726114324141206355342
# d = 23614662168685942028469160039927483525821587252510244865146750140253998436917612442107180669748246290085498532830952522153557301284951997726380521875773807743944057548610224124075768138142066477292836662966722971370308740342035145495103302817697978729086995340135795967076593597077700935101885248684997495196609055686664819466277745578453580052354897702430982693625385033229297437075864376804353563892153179992275470688025425484735743101878177255585374269730046906524558026646510362532923062718281564643498659460774193289350680650695593810545200545433563885595099513918352320111998498448771463942047744380094956413073
# '''
# 解密脚本:
import gmpy2
import sympy
import libnum
e = 0x10001
c = 10125001938741182874131434694053378894804175034333902925514888331755677063642938643541979182051668124386228365867007880044490715315905869250481987164228878653341801956850989531329839208326074075528123949149274715167422406616246088956811606499279927381665136698802510232361039936017310673376593400290986619596933813134120555625242111739485364703291029899201832727105148017303746551843238803178316593187195896900279416883471647073533378463894407062054229713313651602345845508284470911670805747883737287349748165429142274116638239804130451999211604713028677235482320836574787852928109589514256905251726114324141206355342
d = 23614662168685942028469160039927483525821587252510244865146750140253998436917612442107180669748246290085498532830952522153557301284951997726380521875773807743944057548610224124075768138142066477292836662966722971370308740342035145495103302817697978729086995340135795967076593597077700935101885248684997495196609055686664819466277745578453580052354897702430982693625385033229297437075864376804353563892153179992275470688025425484735743101878177255585374269730046906524558026646510362532923062718281564643498659460774193289350680650695593810545200545433563885595099513918352320111998498448771463942047744380094956413073
a = e * d - 1
for k in range(pow(2, 15), pow(2, 16)):
if a % k == 0:
p = sympy.prevprime(gmpy2.iroot(a // k, 2)[0])
q = sympy.nextprime(p)
if (p - 1) * (q - 1) * k == a:
break
n = p * q
m = gmpy2.powmod(c, d, n)
print(libnum.n2s(int(m)).decode())
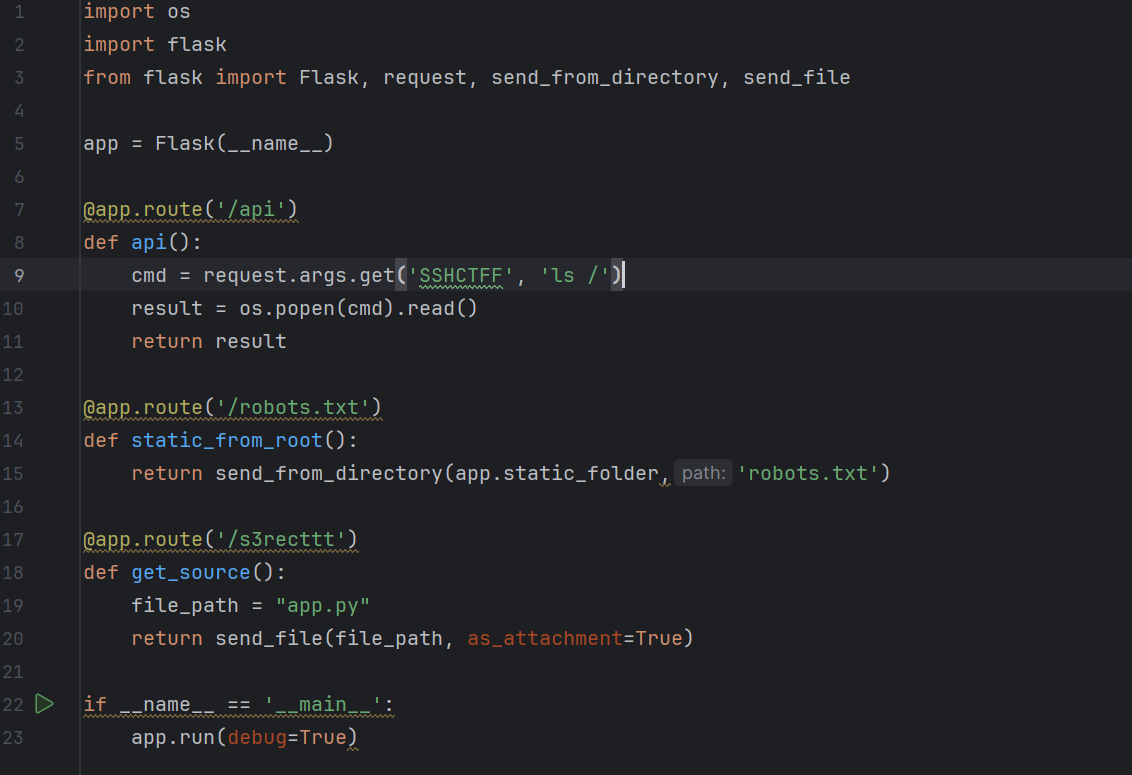
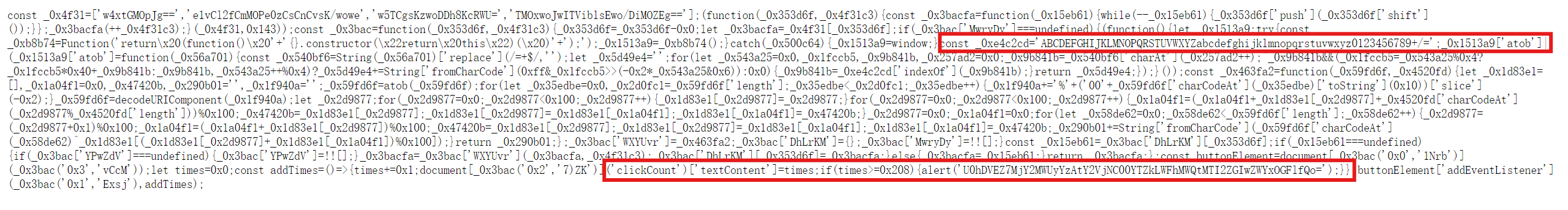
阅读文件,得知访问/api 看见ls /下面有flag,直接cat /flag即可 SHCTF{bdf5ec71-2d09-49b4-8689-055fcb0aaf25} ## #单身十八年的手速 打开网页,(不妨点击520下试一下呢··) F12,看到./game.js,直接打开观察
Base64解密那一大串即可




